Getting Ready for an Audit – 5 Tips from an Auditor
Imagine its audit season and nobody shows up!
Getting audited can be a stressful time. Especially since everyday business operations tasks don’t stop during audit season. While audits can be time consuming, they can be a positive experience and a great opportunity for a business to advance in its cyber security journey. Understanding the benefits of an audit and how to best prepare for it are the keys to a smooth process and positive outcomes.
What is Cyber Security Auditing
A cyber security audit is the review and evaluation of security control implementations against a selected criterion, such as a regulatory framework, a standard, or a minimum baseline configuration often referred to as a benchmark. An audit can be conducted as an internal review where the reviewer should be independent from the function that is to be audited to ensure neutrality. Organisations may also consider contracting an external auditor for expert insights and extra credibility when it comes to compliance auditing.
The purpose of an audit is often to achieve compliance in addition to getting insights into the organisation’s security posture. This includes the identification of vulnerabilities as well as gaps between current implementations and desired state.
The outcome of an audit is the identification of actions to improve security controls and thereby strengthening an organisation’s defenses from experiencing adverse events such as a data breach.
An audit often includes multiple of the following elements:
- Review of technical security control implementation across domains such as infrastructure, access controls, as well as incident detection and remediation capabilities.
- Review of policy and procedure documentation alignment with factors such as business objectives, regulatory requirements, and technical control implementation.
Audit Phases
The following are typical phases of an audit:
Planning and scoping: This phase includes the definition of the audit scope as well as timelines. The scope should include which systems or business units are included in the audit as well as the chosen criteria which may be tied to compliance requirement.

Evidence collection: Depending on the audit approach, the neutral internal party or external auditor collaborates with the relevant business unit to evaluate the implementation of controls against defined criteria. This involves gathering evidence such as system documentation, policies, and standards, architectural documents, security configurations, vulnerability scans, as well as evidence of personnel security awareness training to demonstrate overall security culture.
Findings Analysis: This stage involves identifying the organisation’s compliance with audit criteria often tied to a control framework, maturity model, or compliance standard. During this phase, documents are reviewed to ensure they are current, fit for purpose, and aligned with practical implementations and industry standards. Additionally, security controls are examined through a review of technical configurations to assess their alignment with system criticality and data sensitivity levels and industry better practices. Control gaps are identified during this phase.
Reporting: During this phase the above findings are formalised into a report with gap closure statements for future planning with the aim of continuous improvements. An audit report should link every finding to an action to achieve alignment with the intent of the security control.
How to Get Ready for your Audit
1. Get onboard with the Audit
Getting into the right mindset can make all the difference. This includes looking at the audit from a different angle. Instead of a what can I do for the audit or how to just pass the audit, think:
“What can the Audit Do for Me?” Try to see past the word ‘mandatory’ and assess why this audit is important. How can it benefit YOUR business and cyber security objectives?
Audits are often perceived as a judgement if controls are not met across the board. The reality is an audit is not about proving that your cyber security practices are perfect but rather that you are on a journey of continuous improvement. Deficits in technical control implementation aren’t always a reflection of lack of dedication of the technical team but are commonly related to lack of resources and budgeting. Businesses often tend to invest in programs that are directly linked to the main business function or to advance the business’s mission. Cyber security often receives the short end of the stick when it comes to budget and resource allocation. An audit can support your case, a mandatory requirement can become your best argument, and the auditor can become your greatest ally.
2. Get stakeholders on board
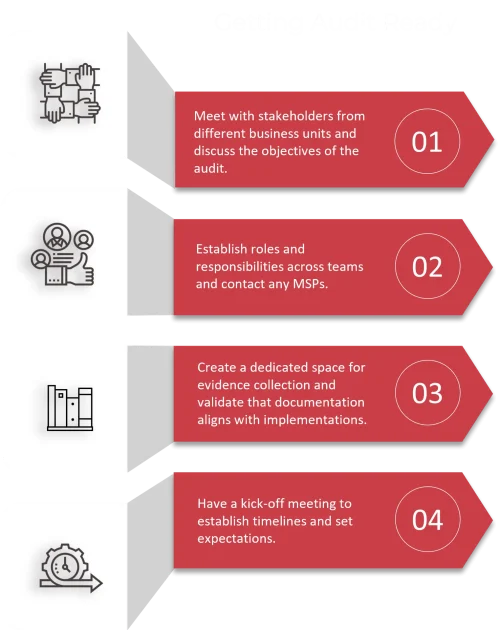
Meet with stakeholders from different business units to understand their challenges and cyber security objectives. For a smooth audit it is essential that all stakeholders understand the reason behind the audit, the benefits, as well as roles and responsibilities in the process such as evidence collection.
Honesty is key and it is important to get the message across the team. Highlight the factor of opportunities for improvement rather than the need to defend your current state.
This can also be a good time to review the control set and help the team understand the intent of the controls the organisation is assessed against.
Different organisational roles bring different contributing factors to the audit. Knowing the right contact person for a particular area of expertise can help to keep the audit on track of timeframes This is how each role can be involved and what they need to bring to the table:
- Executive Leadership Team (ELT): The ELT’s involvement sets the tone for cyber security importance. Their commitment is the defining factor of a successful or unsuccessful audit. The ELT can provide a clear understanding of the organisation’s risk tolerance and priorities as well as provide resources for the audit process and control implementation.
- Information Communications Technologies (ICT) Team and Cybersecurity Team: The technical team plays a central role in the audit process and in the implementation of security controls before, during or after the audit. The tech team usually has the best understanding of current control implementation and challenges. They are the best contact for technical evidence gathering such as configurations reviews, vulnerability scan reports, and past incident reports, as well as technical documentation such as Standard Operating Procedures (SOPs).
- Chief Information Officer (CIO): As part of leadership and ICT, the CIO brings a clear vision for cybersecurity in alignment with organisational goals and risk tolerance. Similar to the ELT, the CIO should be the audit’s greatest supporter, ensuring that the team understand the audit’s significance to achieving security goals as well as allocating the appropriate resources.
- IT Help Desk/Support Teams: Provides valuable insights into user access and security behaviours and might be able to provide insights into topics such as user-password hygiene and patterns in end-user concerns that could be potential indicators of compromise (IOCs) or breach attempts.
- Governance, Risk, and Compliance (GRC) Team as a subset of the Infosec/Cyber team: The GRC analysts should be involved during and after the audit and assist in assessing and managing risk. The Risk Management Team brings insights about the current risk register in relation to cyber security risk as well as business continuity. Similar to the audit team, they can clarify questions in relation to current risks and how risks are currently mitigated or planned. The GRC Team also brings an understanding of strategic planning and essential documentation to support strong cyber security practices. They often work closely together with the technical cyber security team.
- Legal Team: In some cases, it may be beneficial to clarify with the legal team that legal and regulatory requirements are met and that third party vendor contracts are aligned with such legal requirements.
- Human Resources (HR): If you are reviewing employment contracts for cybersecurity requirements, you may need to get into contact with HR. They also often hold information on employee training records for cyber security training programs as well as onboarding procedures.
- Operational/Business Units: Managers of general business areas come with an understanding of how operations rely on data and systems and identify critical assets. They may be able to share valuable insights on vulnerabilities that might require addressing, operational technologies, devices, non-standard or legacy systems that might pose a risk or that may be discovered during an audit.
- Internal Audit: Work with your internal auditor to clarify questions around the process and procedures for auditing security controls. Internal auditors can also give insights on findings that stood out previously and advise on any outstanding items or mitigation efforts. Understanding the status of previous findings is crucial prior to commencement of the audit.
- Finance: Can bring insight into cost arising from cybersecurity incidents in comparison to costs related to the investment of security tools and resources. Finance sometimes has better insights into spending capabilities when it comes to mitigation of security shortcomings.
3. Contact your Managed Service Provider(s) early
If a large part of your technology or identity management services have been outsourced to a managed service provider (MSP), organise a meeting to prepare and set expectations. MSPs often have many clients and audits often occur in specific timeframes, so there is a good chance that your MSP will be busy helping a range of clients. Giving your MSP a heads up about the upcoming audit, and discussing timeframes, documentation/evidence that they will need to provide, as well as availability, can greatly support your audit timeframes and effectiveness, preventing the occurrence of additional costs.
4. Review previous audit findings and documentation
If this has not been your first audit, take the time to review findings from previous audits. Have previous audit findings been addressed? If not, identify the reason why and what is needed to address findings moving forward to show your commitment to continuous improvement.
This is also a good time to review that other relevant documentation is up-to-date, and to store relevant documents in easily accessible central location. When reviewing documents relevant to the audit, it is important to look for alignment with technical implementation. For example, if your access control policy says that MFA must be implemented, validate that this aligns with the actual configurations in place.
Consider creating a dedicated space such as a Share Point site that is accessible to the team(s) involved in the audit. Start collating documentation and technical evidence such as vulnerability scan outputs, records of processes, policies, standards, and procedures. Depending on your familiarity with the control framework, your evidence may be sorted into folders that link directly to the control that is to be assessed.
Be aware of security risks during your audit. Since you are gathering a lot of critical information about your business’s security controls and potential weaknesses, ensure you are protecting your document share location from unauthorised access and data exfiltration to avoid risks of data leakage and consequential security risks associated with reconnaissance techniques and the information gathered on system weaknesses.
5. Talk to the Audit Team prior to the start of the Audit
If your audit has been outsourced to a third-party consultancy, make sure to arrange a kick-off meeting early to establish timelines, method for file sharing and what stakeholders are required. During the meeting, work with the audit team to set clear expectations for both parties on timelines and stakeholder involvement, including potential workshop dates and MSPs involved. Once your timeline is established, book in workshops as soon as possible especially if third party MSPs are required. Ask the auditor to provide you with an initial evidence request list to help you prepare documentation ahead of time to allow for clarifying question and a smooth start.
Summary
When getting ready for an audit, it is crucial to have everyone on board working together as a team to achieve positive outcomes. Breaking the process down into smaller steps can help to make it less overwhelming. It’s even better if you have a security consultant that you can trust and who can guide you through the process step by step.
Below is a high-level break down of the Audit preparation process.
Ready to turn audit season into a strategic advantage?
If you’d like expert guidance, support preparing your evidence, or a partner who can help you strengthen your security posture year‑round, our team is here to help.